Feb 3, 2020
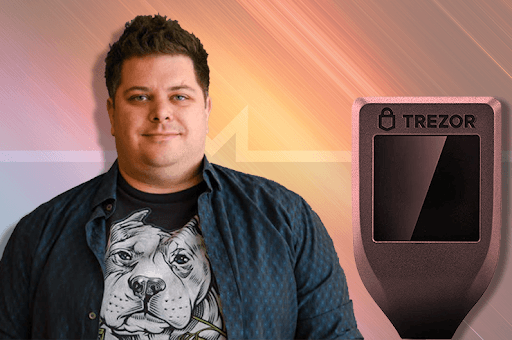
Monero’s Riccardo Spagni Asserts Trezor Prone To ‘Glitching Attacks’
Shailesh is an ardent follower of the crypto world and keenly watches every development taking place in the cryptocurrency space. He loves to voice his opinions through well-curated blogs and articles, which throw light on different facets of the crypto industry.